The invite step is the slowest one
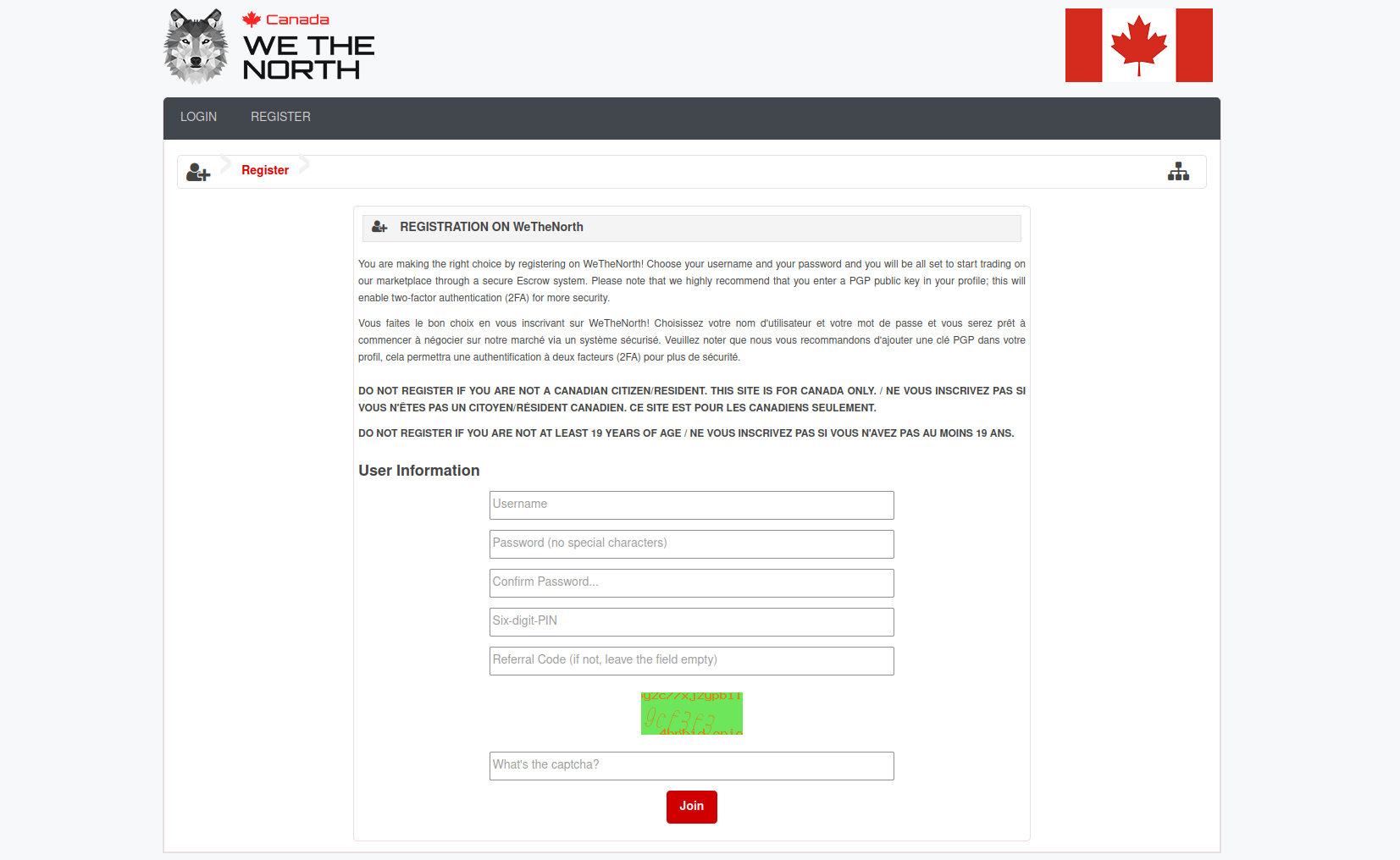
Every WTN registration requires an invitation code from an existing member in good standing. Unlike setting up Tor Browser or generating a PGP key, you cannot self-complete this step. The invite comes from another person, and that person's decision timeline is out of your control.
The fastest path is building a Dread account first. Dread is the primary darknet forum where WTN community threads are active. Post substantively in WTN-related threads, demonstrate that you understand how the platform works, and requests from that position get faster responses than cold approaches from brand-new accounts.
Some long-tenure WTN members post in dedicated Dread threads when they have invite codes to offer. These threads appear periodically and are not continuous. Watch for them rather than messaging established members cold — unsolicited invite requests are a known social engineering vector and members recognize them as such.